December 5th, 2025 by admin
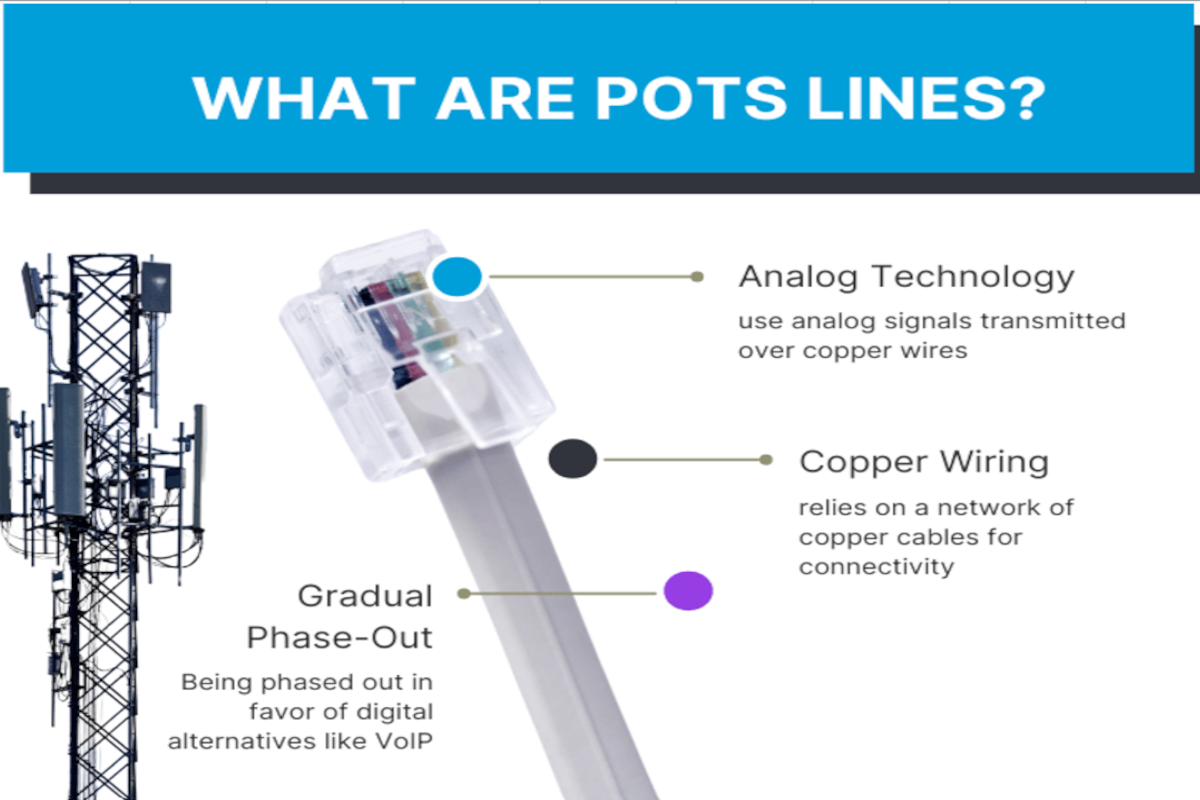
For decades, POTS (Plain Old Telephone Service) lines have powered essential building systems—fax machines, fire alarms, security panels, elevator phones, gate access systems, and more. But today, organizations relying on these legacy analog lines...
Read Full Story »
Tags: best connectivity, business phone system, phone lines
Posted in: Phone System
December 1st, 2025 by admin
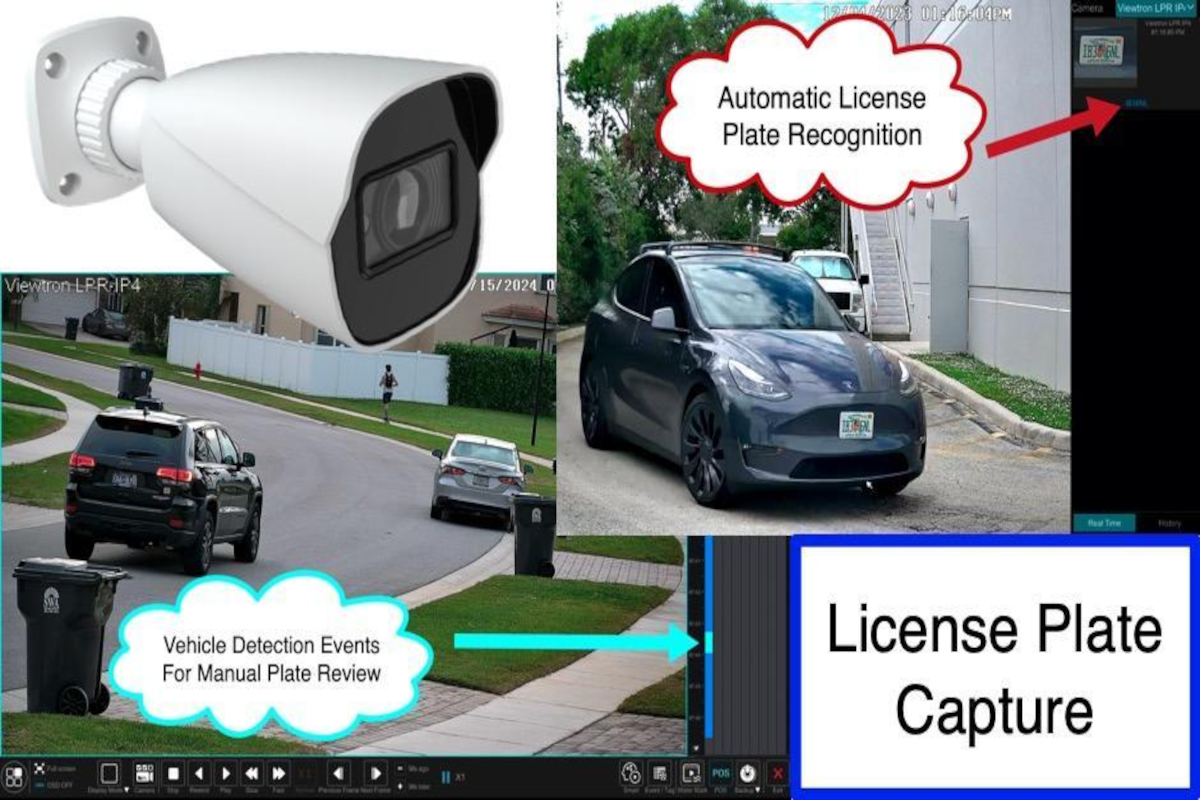
Security threats are evolving—and so should the way we protect our businesses, communities, and properties. Traditional cameras are valuable, but they often fail to deliver the level of detail necessary to identify vehicles, track incidents, and...
Read Full Story »
Tags: cameras, protect my data, video surveillance
Posted in: Security
November 20th, 2025 by admin
Automating Expense Reporting for Business Efficiency
Managing business expenses can feel like a never-ending chore. Receipts pile up, spreadsheets get messy, and approvals drag on. Meanwhile, your employees wait for reimbursements and wonder whether...
Read Full Story »
Tags: best practices, business continuity, expanding business, technology solution
Posted in: IT Solutions
November 13th, 2025 by admin
Why Is the Private Cloud Regaining Traction?
Hybrid cloud strategies that blend the best of public and private environments give businesses the flexibility they need. Not every workload belongs there, though.
As organizations evolve their cloud infrastructure...
Read Full Story »
Tags: backup, best practices, cloud
Posted in: Cloud Computing (Hosting & Colocation), Communications
November 6th, 2025 by admin
How a Routine HP Update Went Off the Rails
HP's OneAgent software is a background tool that manages systems and firmware updates across HP devices. Earlier this month, HP released version 1.2.50.9581 of the software, which included a cleanup script...
Read Full Story »
Tags: data storage, disaster prevention, microsoft
Posted in: Security, Telecommunications
October 30th, 2025 by admin
What Happened in the Prosper Data Breach?
Prosper Marketplace confirmed that attackers gained unauthorized access to its systems, which contain the personal user information for millions of customers. While the company has not disclosed the exact...
Read Full Story »
Tags: data backup, network protection, network security
Posted in: Data Backup & Disaster Recovery, Cyber Security
October 23rd, 2025 by admin
IT: The Unsung Hero of Everyday Efficiency
IT is the backbone of every successful business. With smart technology for business efficiency in place, things run smoothly.
But the wheels start to come off the bus when systems are outdated or poorly...
Read Full Story »
Tags: best practices, network communications, productivity
Posted in: Business Solutions
October 16th, 2025 by admin
OAuth App Attacks Explained
OAuth is a convenient and widely trusted technology that allows users to access applications using accounts like Google or Microsoft. It eliminates the need to type a password.
In OAuth application abuse cases, threat...
Read Full Story »
Tags: backup, communication, network protection
Posted in: Cyber Security
October 9th, 2025 by admin
Customers Expect Convenience
Today's customers expect instant access to information and immediate options for action. From reserving a dinner table to scheduling home repairs, people prefer companies that allow them to book appointments anytime,...
Read Full Story »
Tags: business communications, technology solution, technology
Posted in: Solution
October 2nd, 2025 by admin
The Paper Problem: Why "Old School" Isn't Always Efficient
Paper has a certain comfort to it. It feels familiar, dependable, and easy to manage. That is, until it's not.
Think about how much time your team spends printing, filing, scanning, or...
Read Full Story »
Tags: best practices, data, efficiency
Posted in: Technology